Editorial
APIs power modern apps but can often be exposed to attacks. Proper authentication, encryption, and …
Remote work is flexible but can be risky. Weak home networks, personal devices, and phishing emails…
Not all cyber threats come from outside. Some risks come from staff or ex-employees. Learn how to d…
Passwords can be weak and are often stolen. Passwordless login uses biometrics and secure codes to …
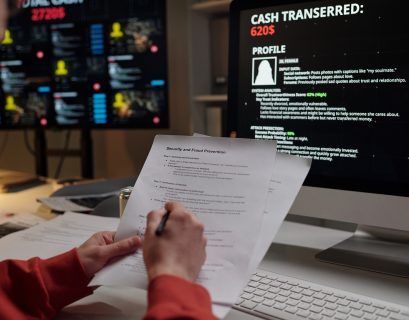
AI is helping businesses grow, but cyberattackers now use it to create scams, automate hacks, and t…
After any cyber incident, organizations need to get answers fast. Forensic readiness helps you coll…
Cloud tools are powerful. However, one missed setting can expose confidential data. The steps conta…
Ransomware is not only about paying money. It is about losing time, trust, and control. Resilience …
Hospitals and clinics hold life-changing data and rely on systems that are “always-on”.…
Zero Trust helps organizations prevent “trusted” access from becoming an open door. This guide expl…